Tag: enabled
Apple Details What to Do If You Can’t Update HomePod When Advanced Data Protection Is Enabled

To use Advanced Data Protection for iCloud, all the devices logged into your Apple ID require a minimum software version. That includes HomePod speakers, which must be running at least HomePod software 16.2.
However, according to Bloomberg‘s Mark Gurman, there is a bug in the Home app that prevents HomePods running older versions of the software from being updated if iCloud end-to-end encryption has been turned on.
This means anyone buying a HomePod that ships with an OS older than 16.2 won’t be able to set it up, because doing so first requires an update.
Apple’s support document explains what options are available to customers facing this predicament. If the speaker in question is a HomePod mini, users can connect it to a Mac via the USB-C cable and update it through Finder (or iTunes on a PC) by selecting the HomePod in the Finder sidebar and clicking the Restore HomePod option. This will update the speaker to the latest software, after which it can be properly set up.
The full-size first-generation HomePod and the new 2023 HomePod have no USB-C port, so unless Apple includes a fix in iOS 16.3, which is expected to be released next week, owners of these speakers will have to temporarily turn off Advanced Data Protection to update the HomePod software. Apple outlines how to do that in the following way:
- Turn off Advanced Data Protection in iCloud settings on your iPhone, iPad, or Mac: In Settings or System Settings, tap your name, then tap iCloud. Scroll to Advanced Data Protection and turn off Advanced Data Protection.
- If you received an error message when you previously tried to set up your HomePod, you may need to reset your HomePod. Then set up your HomePod.
- Update your HomePod to the latest software using the Home app.
- Turn on Advanced Data Protection in iCloud settings on your iPhone, iPad, or Mac: In Settings or System Settings, tap your name, then tap iCloud. Scroll to Advanced Data Protection and turn on Advanced Data Protection.
Apple advises anyone who temporarily turns off Advanced Data Protection to turn it back on immediately after their HomePod software is updated.
This article, “Apple Details What to Do If You Can’t Update HomePod When Advanced Data Protection Is Enabled” first appeared on MacRumors.com
Discuss this article in our forums
Meta’s new ad system addresses allegations that it enabled housing discrimination

Meta’s launching a new ad distribution system in the US as part of the settlement it reached with the US Department of Justice (DOJ) last year. In an announcement on its site, Meta says its new Variance Reduction System (VRS) will create a more “equitable distribution of ads” on the company’s platforms, addressing claims that the platform propagated housing discrimination by letting advertisers exclude protected groups from their marketing campaigns.
Meta has contended with these kinds of accusations for years, dating back to a 2016 report from ProPublica that reveals how advertisers could shut out users based on their race.
Things came to a head when the Department of Housing and Urban Development (HUD) filed a lawsuit against the…
Expanded iCloud Encryption Can’t Be Enabled From New Apple Devices Right Away
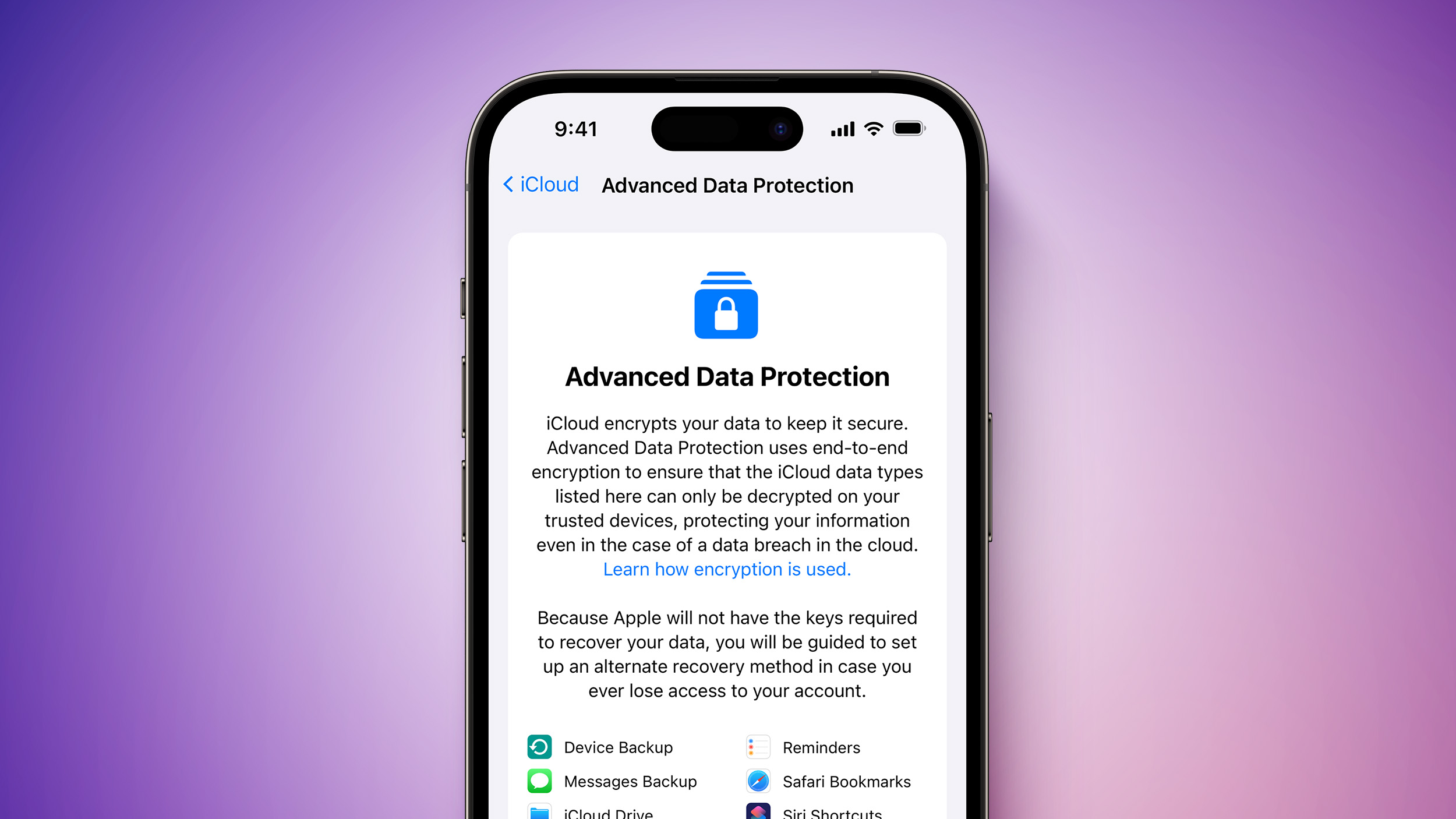
To protect users, Apple does not allow Advanced Data Protection to be enabled from a brand new device for an unspecified period after the device was first set up and added to a user’s Apple ID account. We have seen dates range from late January to early February for when users will be able to turn on the feature from a new device. This buffer helps to prevent a malicious actor from enabling the feature if a user is hacked.
Users can still enable Advanced Data Protection from an older device they added to the same Apple ID account, such as another iPhone, iPad, or Mac. In this case, all devices added to that Apple ID account are fully protected by the expanded end-to-end encryption for iCloud, including newer ones that are still in the waiting period.
Excuse me, what?
Anyone else? pic.twitter.com/JVRm91Xzbd
— Will Sigmon (@WSig) December 7, 2022
Turning on Advanced Data Protection removes your encryption keys from Apple’s servers for the iCloud categories protected by the feature, ensuring that your data remains secure even in the case of a data breach in the cloud. When the feature is enabled, the encryption keys are only stored on your trusted Apple devices, meaning that they cannot be accessed by Apple or others. The feature can be turned off at any time, at which point your devices will securely upload the encryption keys to Apple’s servers again.
When Advanced Data Protection is enabled, access to your data via iCloud.com is disabled by default. Users can turn on data access on iCloud.com, which allows the web browser and Apple to have temporary access to data-specific encryption keys.
iCloud already protects 14 data categories using end-to-end encryption by default, without Advanced Data Protection enabled, including passwords stored in iCloud Keychain, Health data, Apple Maps search history, Apple Card transactions, and more. Apple has a support document with a chart detailing what is protected by standard levels of encryption and what is protected by Advanced Data Protection when enabled.
Advanced Data Protection is available for U.S. users only at launch and will start rolling out to the rest of the world in early 2023, according to Apple. For more details about the feature, read our coverage of Apple’s announcement earlier this week.
This article, “Expanded iCloud Encryption Can’t Be Enabled From New Apple Devices Right Away” first appeared on MacRumors.com
Discuss this article in our forums
Did you know one of Overwatch’s handiest PvE features can be enabled in Overwatch 2’s PvP?

There have been some fairly unpopular changes to the way Overwatch 2 does its UI. Whether its the options menu being moved to a more difficult-to-find place on the main menu, or the lack of feedback cards at the end of a round, it’s safe to say Blizzard hasn’t really nailed the landing with UI and UX on the new game.
But for all the teething problems, there are some bonuses, too. Take the option to enable the “Play Sound When Teammate Eliminated” setting in the audio options. It might sound horrible (spoiler: it is!) but when you’re ankles-deep in the melee around a control point, sometimes you just need the short, sharp trill of an emergency siren to let you know that ‘yep, that Tracer is down again’.
I picked up the tip from PC Gamer yesterday, and after playing a few games last night, I have to say: this could be game-changing for me! I primarily play support (thank me later), and knowing that the tank I had just been healing is finally down the second I turn away without having to do the little radial scan of the screen is great. It frees me up to instantly start buffing that Widowmaker I know has an Ult nearly ready to go.
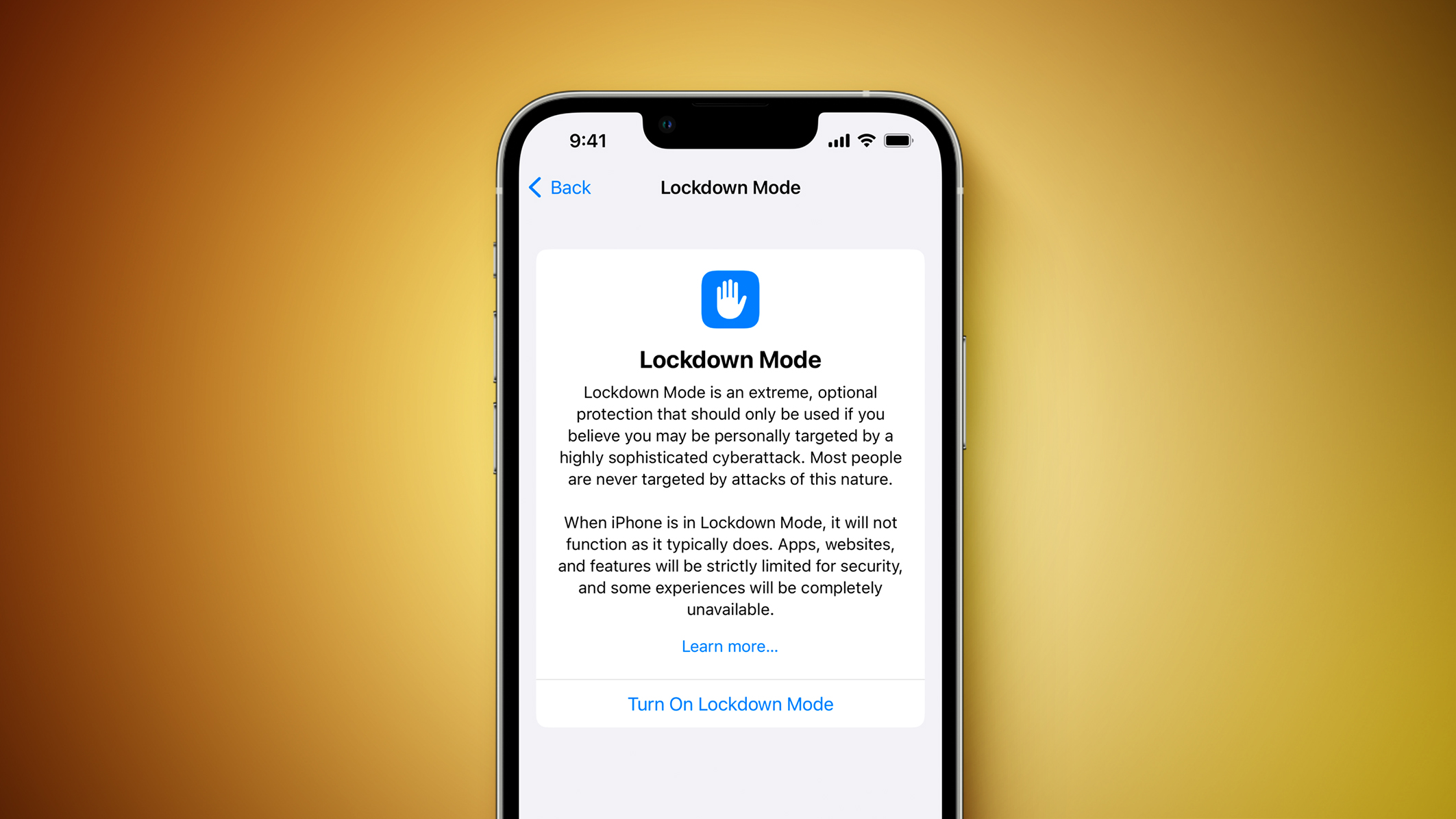
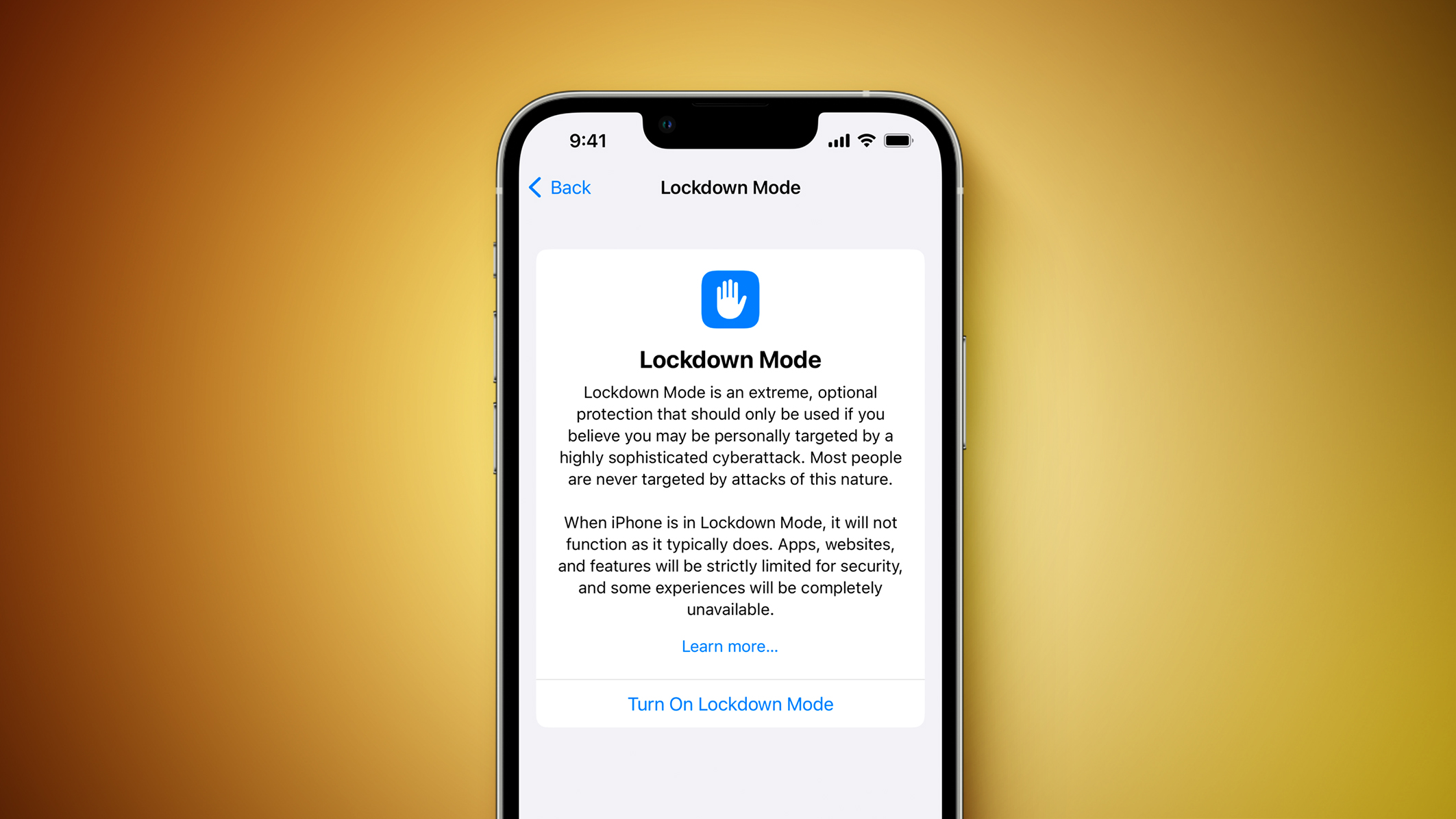
iOS 16 VPN Tunnels Leak Data, Even When Lockdown Mode Is Enabled
Speaking to MacRumors, security researchers Tommy Mysk and Talal Haj Bakry explained that iOS 16’s approach to VPN traffic is the same whether Lockdown mode is enabled or not. The news is significant since iOS has a persistent, unresolved issue with leaking data outside an active VPN tunnel.
In August, it again emerged that third-party VPNs for iOS and iPadOS routinely fail to route all network traffic through a secure tunnel after they have been turned on – an issue that Apple has purportedly known about for years.
Typically, when a user activates a VPN, the operating system closes all existing internet connections and then re-establishes them through the VPN tunnel. In iOS, security researchers have found that sessions and connections established before the VPN is turned on are not terminated as one would expect, and can still send data outside the VPN tunnel while it is active, leaving it potentially unencrypted and exposed to ISPs and other parties.
According to a report from privacy company Proton, an iOS VPN bypass vulnerability had been identified in iOS 13.3.1, which persisted through three subsequent updates. Apple indicated it would add Kill Switch functionality in a future software update that would allow developers to block all existing connections if a VPN tunnel is lost, but this functionality does not appear to prevent data leaks as of iOS 15 and iOS 16.
Mysk and Bakry have now discovered that iOS 16 communicates with select Apple services outside an active VPN tunnel and leaks DNS requests without the user’s knowledge:
We confirm that iOS 16 does communicate with Apple services outside an active VPN tunnel. Worse, it leaks DNS requests. #Apple services that escape the VPN connection include Health, Maps, Wallet.
We used @ProtonVPN and #Wireshark. Details in the video:#CyberSecurity #Privacy pic.twitter.com/ReUmfa67ln— Mysk 🇨🇦🇩🇪 (@mysk_co) October 12, 2022
Mysk and Bakry also investigated whether iOS 16’s Lockdown mode takes the necessary steps to fix this issue and funnel all traffic through a VPN when one is enabled, and it appears that the exact same issue persists whether Lockdown mode is enabled or not, particularly with push notifications. This means that the minority of users who are vulnerable to a cyberattack and need to enable Lockdown mode are equally at risk of data leaks outside their active VPN tunnel.
iOS 16 introduced Lockdown mode as an optional security feature designed to protect the “very small number” of users who may be at risk of “highly targeted cyberattacks” from private companies developing state-sponsored spyware, such as journalists, activists, and government employees. Lockdown mode does not enable a VPN itself, and relies on the same third-party VPN apps as the rest of the system.
Update: The Lockdown Mode leaks more traffic outside the VPN tunnel than the “normal” mode. It also sends push notification traffic outside the VPN tunnel. This is weird for an extreme protection mode.
Here is a screenshot of the traffic (VPN and Kill Switch enabled) #iOS pic.twitter.com/25zIFT4EFa— Mysk 🇨🇦🇩🇪 (@mysk_co) October 13, 2022
Due to the fact that iOS 16 leaks data outside the VPN tunnel even where Lockdown mode is enabled, internet service providers, governments, and other organizations may be able to identify users who have a large amount of traffic, potentially highlighting influential individuals. It is possible that Apple does not want a potentially malicious VPN app to collect some kinds of traffic, but seeing as ISPs and governments are then able to do this, even if that is what the user is specifically trying to avoid, it seems likely that this is part of the same VPN problem that affects iOS 16 as a whole.
It is worth noting that Apple only lists high-level features that activate when Lockdown mode is enabled, and Apple has not explicitly mentioned any changes that take place to affect VPN traffic. Nevertheless, as Lockdown mode claims to be an extreme protection measure, it seems like a considerable oversight that VPN traffic is a vulnerable point.
This article, “iOS 16 VPN Tunnels Leak Data, Even When Lockdown Mode Is Enabled” first appeared on MacRumors.com
Discuss this article in our forums
Do we really need a $340, Wi-Fi enabled toaster?
iOS 16 Beta 6: New Battery Percentage Icon Still Not Enabled on Some iPhones
![]()
Since the release of the iPhone X in 2017, and on every iPhone with a notch since, battery percentage has only been visible in Control Center by swiping down on the top-right corner of the display. Apple made headlines last week when it finally made battery percentage visible in the status bar again on iPhones with a notch, eliminating the need to swipe down, but the feature is not supported on all iPhones in the latest iOS 16 betas.
The new icon includes the battery percentage within the icon rather than to the left of it. The white battery icon remains completely filled in until the battery reaches 20% or lower, at which point a fifth of the icon turns red and the rest of the icon becomes translucent. The icon’s current implementation has proven to be controversial, but it’s important to remember that iOS 16 is still in beta and subject to additional changes.
It’s unclear why the new battery percentage icon is not available on some iPhone models with a notch, but the excluded models are either “mini” iPhones or have an LCD display instead of an OLED display. As mentioned, iOS 16 is still in beta testing, so it’s possible that Apple could expand the feature in a future beta release.
Apple is expected to release iOS 16 to all users with an iPhone 8 or newer in September.
This article, “iOS 16 Beta 6: New Battery Percentage Icon Still Not Enabled on Some iPhones” first appeared on MacRumors.com
Discuss this article in our forums