Tag: ‘hijack’
How prompt injection can hijack autonomous AI agents like Auto-GPT
New Ultrasound Attack Can Secretly Hijack Phones and Smart Speakers
The attacks work by modulating voice commands into near-ultrasound inaudible signals so that humans can’t hear them but the voice assistant will still respond to them. These signals are then embedded into a carrier, such as an app or YouTube video. When a vulnerable device picks up the carrier, it ends up obeying the hidden embedded commands. Attackers can use social engineering to trick the victim into playing the sound clip, Xia explained. “And once the victim plays this clip, voluntarily or involuntarily, the attacker can manipulate your Siri to do something, for example, open your door.”
For NUIT-1 attacks, using Siri, the answer is yes. The boffins found they could control an iPhone’s volume so that a silent instruction to Siri generates an inaudible response. The other three voice assistants — Google’s, Cortana, and Alexa — are still susceptible to the attacks, but for NUIT-1, the technique can’t silence devices’ response so the victim may notice shenanigans are afoot. It’s also worth noting that the length of malicious commands must be below 77 milliseconds — that’s the average reaction time for the four voice assistants across multiple devices.
In a NUIT-2 attack, the attacker exploits the speaker on one device to attack the microphone and associated voice assistant of a second device. These attacks aren’t limited by the 77-millisecond window and thus give the attacker a broader range of possible action commands. An attacker could use this scenario during Zooms meeting, for example: if an attendee unmutes themself, and their phone is placed next to their computer, an attacker could use an embedded attack signal to attack that attendees phone. The researchers will publish their research and demonstrate the NUIT attacks at the USENIX Security Symposium in August.
Read more of this story at Slashdot.
Steam Deck giveaway hopefuls hijack Game Awards chat by spamming Linux commands
Researchers Used a Sirius XM Bug to Easily Hijack a Bunch of Different Cars
: Hackers hijack Fast Company, send obscene push alert through Apple News
GPS Jammers Are Being Used to Hijack Trucks and Down Drones
Jammers work by overpowering GPS signals by emitting a signal at the same frequency, just a bit more powerful than the original. The typical jammers used for cargo hijackings are able to jam frequencies from up to 5 miles away rendering GPS tracking and security apparatuses, such as those used by trucking syndicates, totally useless. In Mexico, jammers are used in some 85% of cargo truck thefts. Statistics are harder to come by in the United States, but there can be little doubt the devices are prevalent and widely used. Russia is currently availing itself of the technology to jam commercial planes in Ukraine.
As we’ve covered, the proliferating commercial drone sector is also prey to attack…. During a light show in Hong Kong in 2018, a jamming device caused 46 drones to fall out of the sky, raising public awareness of the issue.
While the problem is getting worse, the article also notes that companies are developing anti-jamming solutions for drone receivers, “providing protection and increasing the resiliency of GPS devices against jamming attacks.
“By identifying and preventing instances of jamming, fleet operators are able to prevent cargo theft.”
Read more of this story at Slashdot.
There was a TikTok Android app exploit that let hackers hijack accounts with one click
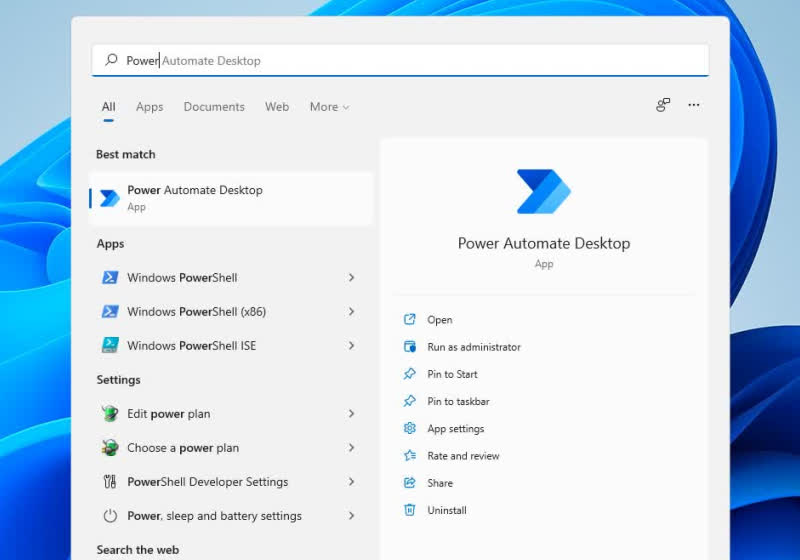
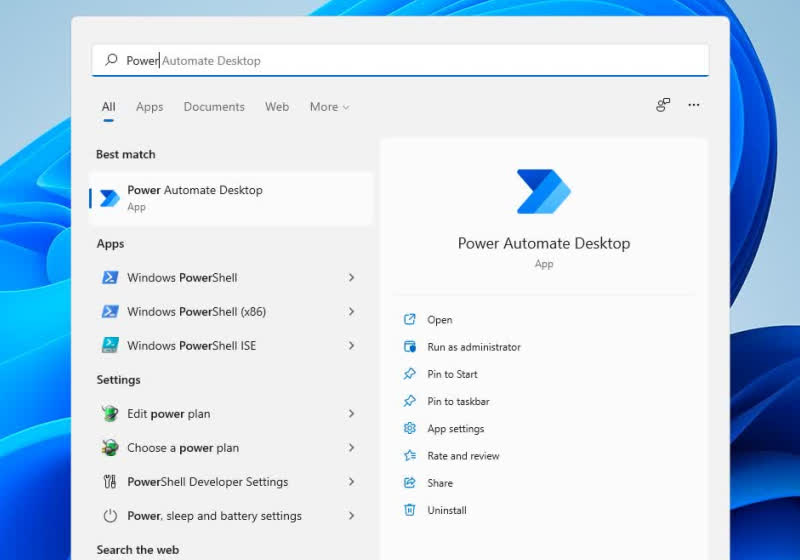
Security researchers successfully hijack Windows 11’s Power Automate tool
Zoom fixes security flaw that let attackers hijack your Mac
Zoom users with Macs can rest a little easier. Ars Technicareports Zoom has updated its Mac software to patch a vulnerability that let would-be intruders take control of systems. The video calling software’s auto-updater software not only had root-level access, but had a signature verification system that you could fool simply by giving your package a familiar file name. A hacker could force your app to downgrade or otherwise enable exploits.
Objective-See Foundation (OSF) creator and researcher Patrick Wardle first discovered the security hole, and disclosed it to Zoom in December last year. Zoom fixed that problem, but introduced another bug in the process. Zoom addressed that, too, but Wardle found still another flaw. The OSF founder discussed his findings at Def-Con last week. Zoom acknowledged the issue that day, and patched it afterward.
This isn’t the first time Zoom has grappled with security headaches, including for the Mac. In 2019, the company raced to fix a webcam hijack exploit that relied on a locally-created web server. Increased scrutiny of Zoom at the start of the COVID-19 pandemic in spring 2020 also prompted a full-scale review of the company’s practices. While that did lead to changes, it’s clear Zoom isn’t immune to missteps.