LastPass warns of imposter app in Apple’s App Store
The password manager said the fraudulent app attempts to copy the company’s branding and user interface in order to trick users.
Read more: LastPass warns of imposter app in Apple’s App Store
Computers Tech Games Crypto Music and More
The password manager said the fraudulent app attempts to copy the company’s branding and user interface in order to trick users.
Read more: LastPass warns of imposter app in Apple’s App Store
A fake app that was masquerading as password manager LastPass on the App Store has been removed, whether by Apple or the fake app’s developer is yet unclear — Apple has not commented. The illegitimate app was listed under an individual developer’s name (Parvati Patel) and copied LastPass’s branding and user interface in an attempt […]
© 2024 TechCrunch. All rights reserved. For personal use only.
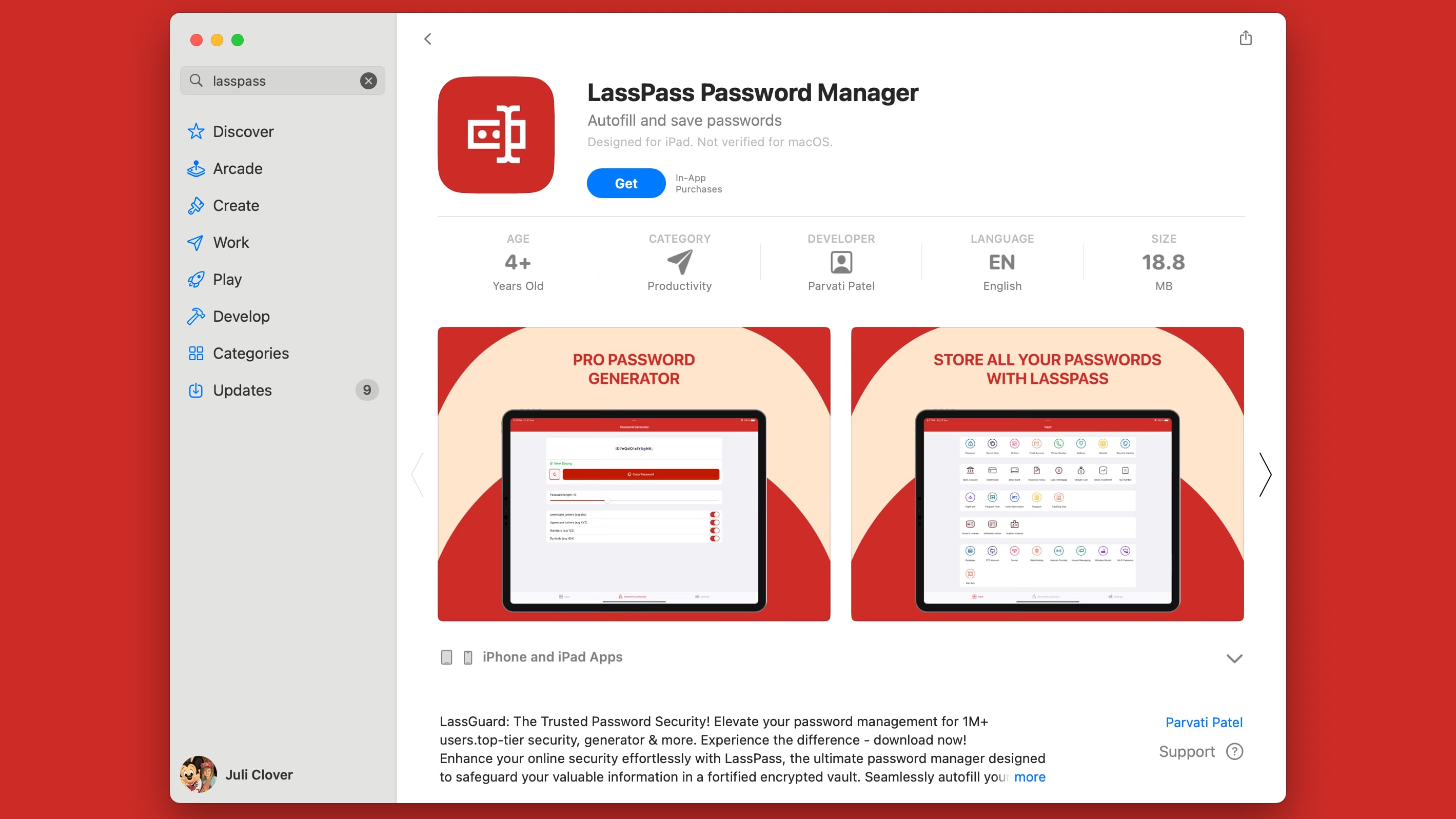
The “LassPass Password Manager” app was somehow approved by Apple’s App Store review team, even though it appears to clearly mimic the LastPass app. It doesn’t use exactly the same icon and the name is a letter off, but the similarities could confuse some LastPass users.
It is unclear if the fake LassPass app is attempting to steal login information from users, but it does have options for adding passwords, email accounts, addresses, bank accounts, credit cards, debit cards, and more. It doesn’t ask for a LastPass login of any kind, but it is possible that the developer can see information added to the app.
There is also a “PRO” upgrade that costs $1.99 per month, $9.99 per year, or $49.99 for a “lifetime” subscription, so the aim of the app may be collecting subscription money from customers. Either way, LastPass users should be aware of the fake app and should avoid it. At best it is aiming to steal money, and at worst, it is stealing passwords and credit card information.
Clone apps often make their way into the App Store, but the app impersonating LastPass is particularly concerning because it could be accessing sensitive information. It is not clear how an app mimicking one of the most popular password management apps was approved by Apple, and its discovery comes at a critical time for the company.
Apple has been promoting the safety and security of the App Store as it prepares to allow for alternate app marketplaces in the European Union, and allowing a fake password management app onto the App Store is not a good look.
LastPass says that it is working to get the clone app removed from the App Store. Though LastPass published its alert yesterday, and presumably contacted Apple at the same time, the app remains in the App Store as of now.
Update 11:00 a.m. Pacific Time: The LassPass app has been removed from the App Store.
This article, “Fake LastPass App Sneaks Past Apple’s Review Team” first appeared on MacRumors.com
Discuss this article in our forums

Beleaguered password manager LastPass has announced yet another serious security screwup and, this time, it may be the final straw for some users.
LastPass worked with incident response experts at Mandiant to perform forensics and found that a DevOps engineer’s home computer was targeted to get around security mitigations. The attackers exploited a remote code execution vulnerability in a third-party media software package and planted keylogger malware on the employee’s personal computer. “The threat actor was able to capture the employee’s master password as it was entered, after the employee authenticated with MFA, and gain access to the DevOps engineer’s LastPass corporate vault,” the company said. “The threat actor then exported the native corporate vault entries and content of shared folders, which contained encrypted secure notes with access and decryption keys needed to access the AWS S3 LastPass production backups, other cloud-based storage resources, and some related critical database backups,” LastPass confirmed. LastPass originally disclosed the breach in August 2022 and warned that “some source code and technical information were stolen.”
SecurityWeek adds: “In January 2023, the company said the breach was far worse than originally reported and included the theft of account usernames, salted and hashed passwords, a portion of Multi-Factor Authentication (MFA) settings, as well as some product settings and licensing information.”
Read more of this story at Slashdot.

