Tag: lockdown
How to Enable Lockdown Mode for Heightened Security on iPhone and iPad
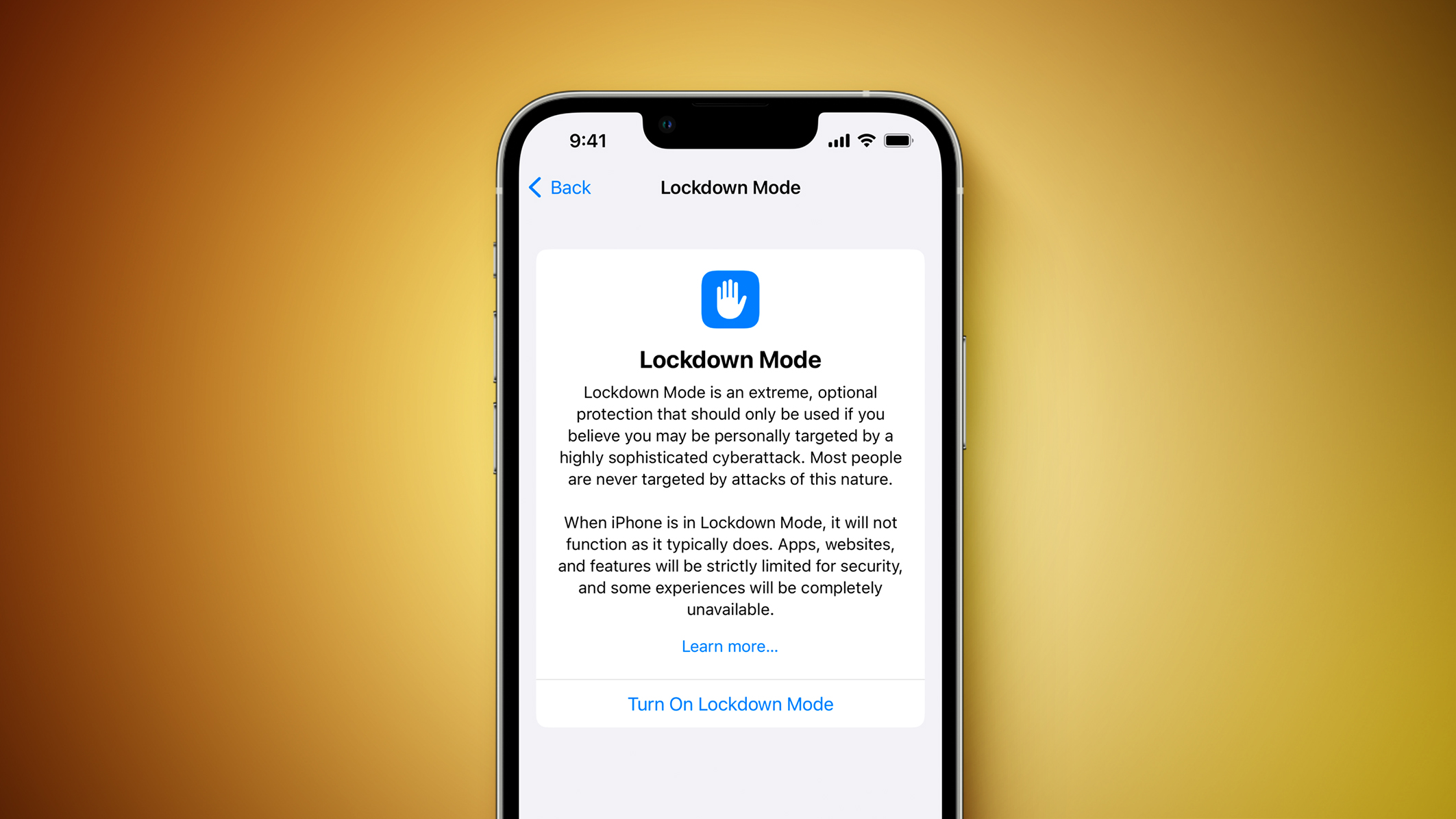
In iOS 16 and iPadOS 16, Apple brought iPhone and iPad users Lockdown Mode, an optional new security feature that’s designed to protect users who may be at risk of highly targeted cyberattacks from private companies developing state-sponsored spyware.
While the feature is aimed at the very small number of users who could be targets of cyberattacks, such as journalists, activists, and government employees, any user can enable it on their device for what Apple calls an “extreme” level of security.
Lockdown Mode Protections
When enabled, Lockdown Mode strictly limits or disables the functionality of features, apps, and websites. Lockdown Mode protections include the following:
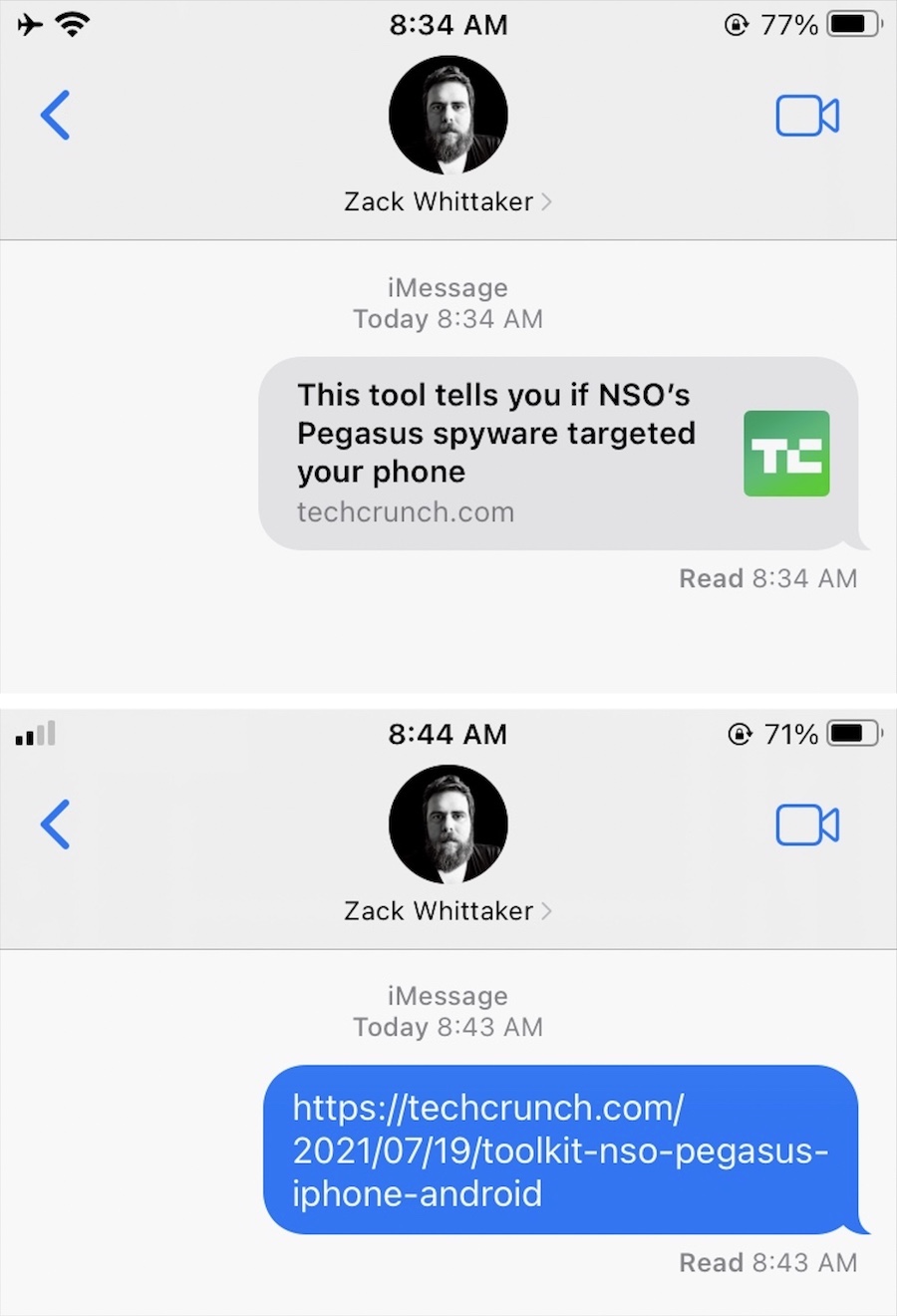
- In the Messages app, most message attachment types other than images are blocked, and some features like link previews are unavailable.
- Incoming FaceTime calls from people you have not previously called are blocked. Incoming invitations for other Apple services from people you have not previously invited are also blocked.
- Some complex web technologies and browsing features, including just-in-time (JIT) JavaScript compilation, are disabled unless the user excludes a trusted site from Lockdown Mode. This protection applies to Safari and all other web browsers using WebKit across the iPhone, iPad, and Mac.
- Shared albums will be removed from the Photos app, and new shared album invitations will be blocked.
- When a device is locked, wired connections with other devices/accessories are blocked.
- Configuration profiles cannot be installed, and the device cannot enroll into mobile device management (MDM), while Lockdown Mode is turned on.
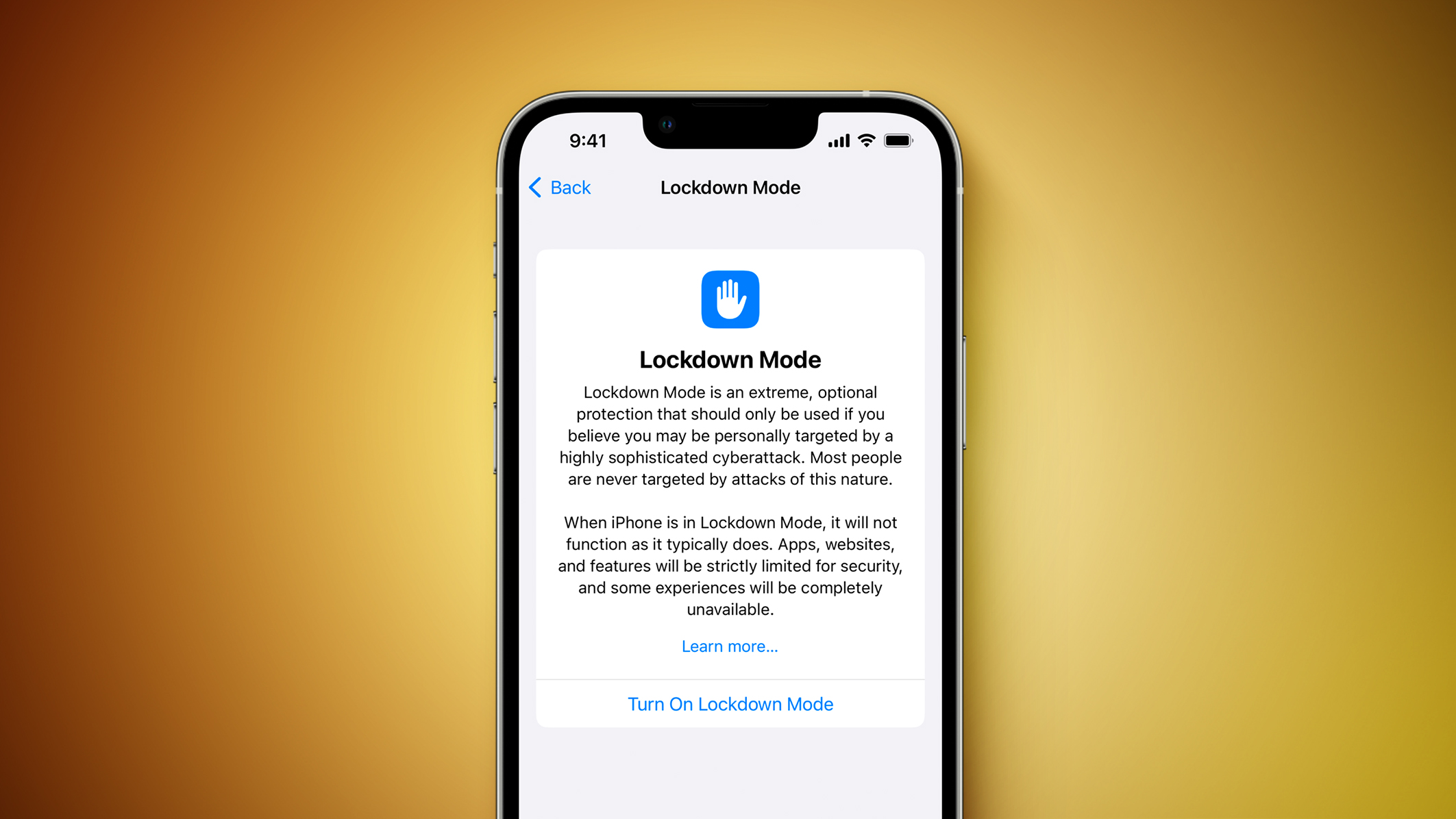
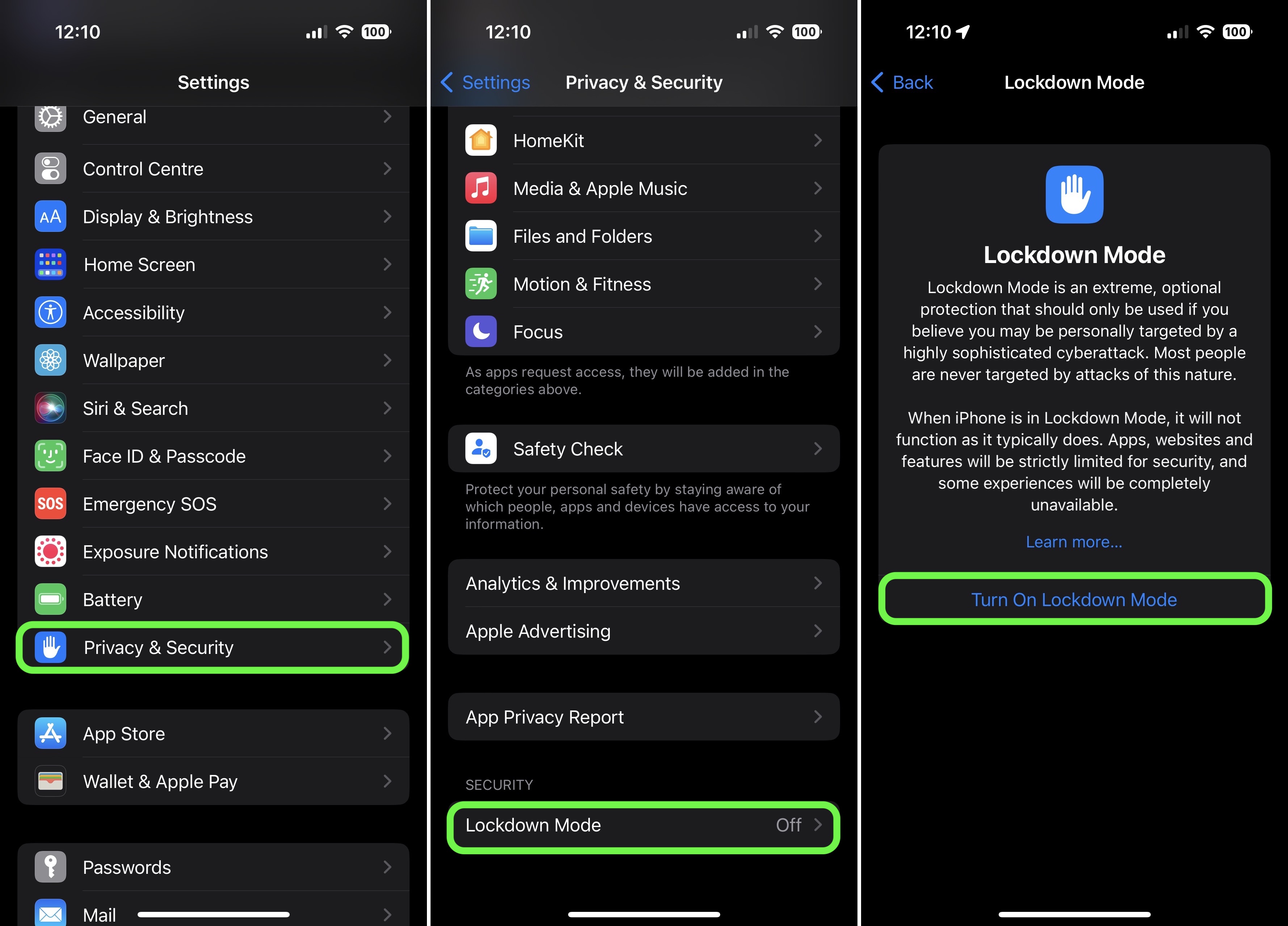
How to Enable Lockdown Mode on iPhone and iPad
Lockdown Mode is turned off by default on iPhone and iPad, but you can enable it by following these steps.
- Launch the Settings app.
- Scroll down and tap Privacy & Security.
- Scroll to the bottom of the menu and under “Security,” tap Lockdown Mode.
- Read the on-screen information, then tap Turn On Lockdown Mode.
- Review the list of protections. If you’re still happy to go ahead, tap Turn On Lockdown Mode.
Apple has added a new category to its Security Bounty program to reward researchers who find Lockdown Mode bypasses and help improve its protections, so expect new protections to be added over time.
This article, “How to Enable Lockdown Mode for Heightened Security on iPhone and iPad” first appeared on MacRumors.com
Discuss this article in our forums
iOS 16 VPN Tunnels Leak Data, Even When Lockdown Mode Is Enabled
Speaking to MacRumors, security researchers Tommy Mysk and Talal Haj Bakry explained that iOS 16’s approach to VPN traffic is the same whether Lockdown mode is enabled or not. The news is significant since iOS has a persistent, unresolved issue with leaking data outside an active VPN tunnel.
In August, it again emerged that third-party VPNs for iOS and iPadOS routinely fail to route all network traffic through a secure tunnel after they have been turned on – an issue that Apple has purportedly known about for years.
Typically, when a user activates a VPN, the operating system closes all existing internet connections and then re-establishes them through the VPN tunnel. In iOS, security researchers have found that sessions and connections established before the VPN is turned on are not terminated as one would expect, and can still send data outside the VPN tunnel while it is active, leaving it potentially unencrypted and exposed to ISPs and other parties.
According to a report from privacy company Proton, an iOS VPN bypass vulnerability had been identified in iOS 13.3.1, which persisted through three subsequent updates. Apple indicated it would add Kill Switch functionality in a future software update that would allow developers to block all existing connections if a VPN tunnel is lost, but this functionality does not appear to prevent data leaks as of iOS 15 and iOS 16.
Mysk and Bakry have now discovered that iOS 16 communicates with select Apple services outside an active VPN tunnel and leaks DNS requests without the user’s knowledge:
We confirm that iOS 16 does communicate with Apple services outside an active VPN tunnel. Worse, it leaks DNS requests. #Apple services that escape the VPN connection include Health, Maps, Wallet.
We used @ProtonVPN and #Wireshark. Details in the video:#CyberSecurity #Privacy pic.twitter.com/ReUmfa67ln— Mysk 🇨🇦🇩🇪 (@mysk_co) October 12, 2022
Mysk and Bakry also investigated whether iOS 16’s Lockdown mode takes the necessary steps to fix this issue and funnel all traffic through a VPN when one is enabled, and it appears that the exact same issue persists whether Lockdown mode is enabled or not, particularly with push notifications. This means that the minority of users who are vulnerable to a cyberattack and need to enable Lockdown mode are equally at risk of data leaks outside their active VPN tunnel.
iOS 16 introduced Lockdown mode as an optional security feature designed to protect the “very small number” of users who may be at risk of “highly targeted cyberattacks” from private companies developing state-sponsored spyware, such as journalists, activists, and government employees. Lockdown mode does not enable a VPN itself, and relies on the same third-party VPN apps as the rest of the system.
Update: The Lockdown Mode leaks more traffic outside the VPN tunnel than the “normal” mode. It also sends push notification traffic outside the VPN tunnel. This is weird for an extreme protection mode.
Here is a screenshot of the traffic (VPN and Kill Switch enabled) #iOS pic.twitter.com/25zIFT4EFa— Mysk 🇨🇦🇩🇪 (@mysk_co) October 13, 2022
Due to the fact that iOS 16 leaks data outside the VPN tunnel even where Lockdown mode is enabled, internet service providers, governments, and other organizations may be able to identify users who have a large amount of traffic, potentially highlighting influential individuals. It is possible that Apple does not want a potentially malicious VPN app to collect some kinds of traffic, but seeing as ISPs and governments are then able to do this, even if that is what the user is specifically trying to avoid, it seems likely that this is part of the same VPN problem that affects iOS 16 as a whole.
It is worth noting that Apple only lists high-level features that activate when Lockdown mode is enabled, and Apple has not explicitly mentioned any changes that take place to affect VPN traffic. Nevertheless, as Lockdown mode claims to be an extreme protection measure, it seems like a considerable oversight that VPN traffic is a vulnerable point.
This article, “iOS 16 VPN Tunnels Leak Data, Even When Lockdown Mode Is Enabled” first appeared on MacRumors.com
Discuss this article in our forums