Tag: malware
Compromised Sites Use Fake Chrome Update Warnings to Spread Malware
The campaign has been underway since November 2022, and according to NTT’s security analyst Rintaro Koike, it shifted up a gear after February 2023, expanding its targeting scope to cover users who speak Japanese, Korean, and Spanish. BleepingComputer has found numerous sites hacked in this malware distribution campaign, including adult sites, blogs, news sites, and online stores…
If a targeted visitor browses the site, the scripts will display a fake Google Chrome error screen stating that an automatic update that is required to continue browsing the site failed to install. “An error occurred in Chrome automatic update. Please install the update package manually later, or wait for the next automatic update,” reads the fake Chrome error message. The scripts will then automatically download a ZIP file called ‘release.zip’ that is disguised as a Chrome update the user should install.
However, this ZIP file contains a Monero miner that will utilize the device’s CPU resources to mine cryptocurrency for the threat actors. Upon launch, the malware copies itself to C:Program FilesGoogleChrome as “updater.exe” and then launches a legitimate executable to perform process injection and run straight from memory. According to VirusTotal, the malware uses the “BYOVD” (bring your own vulnerable driver) technique to exploit a vulnerability in the legitimate WinRing0x64.sys to gain SYSTEM privileges on the device.
The miner persists by adding scheduled tasks and performing Registry modifications while excluding itself from Windows Defender. Additionally, it stops Windows Update and disrupts the communication of security products with their servers by modifying the IP addresses of the latter in the HOSTS file. This hinders updates and threat detection and may even disable an AV altogether.
Read more of this story at Slashdot.
Beware: many ChatGPT extensions and apps could be malware
FBI Warns Against Using Public USB Ports Due to Malware Risk
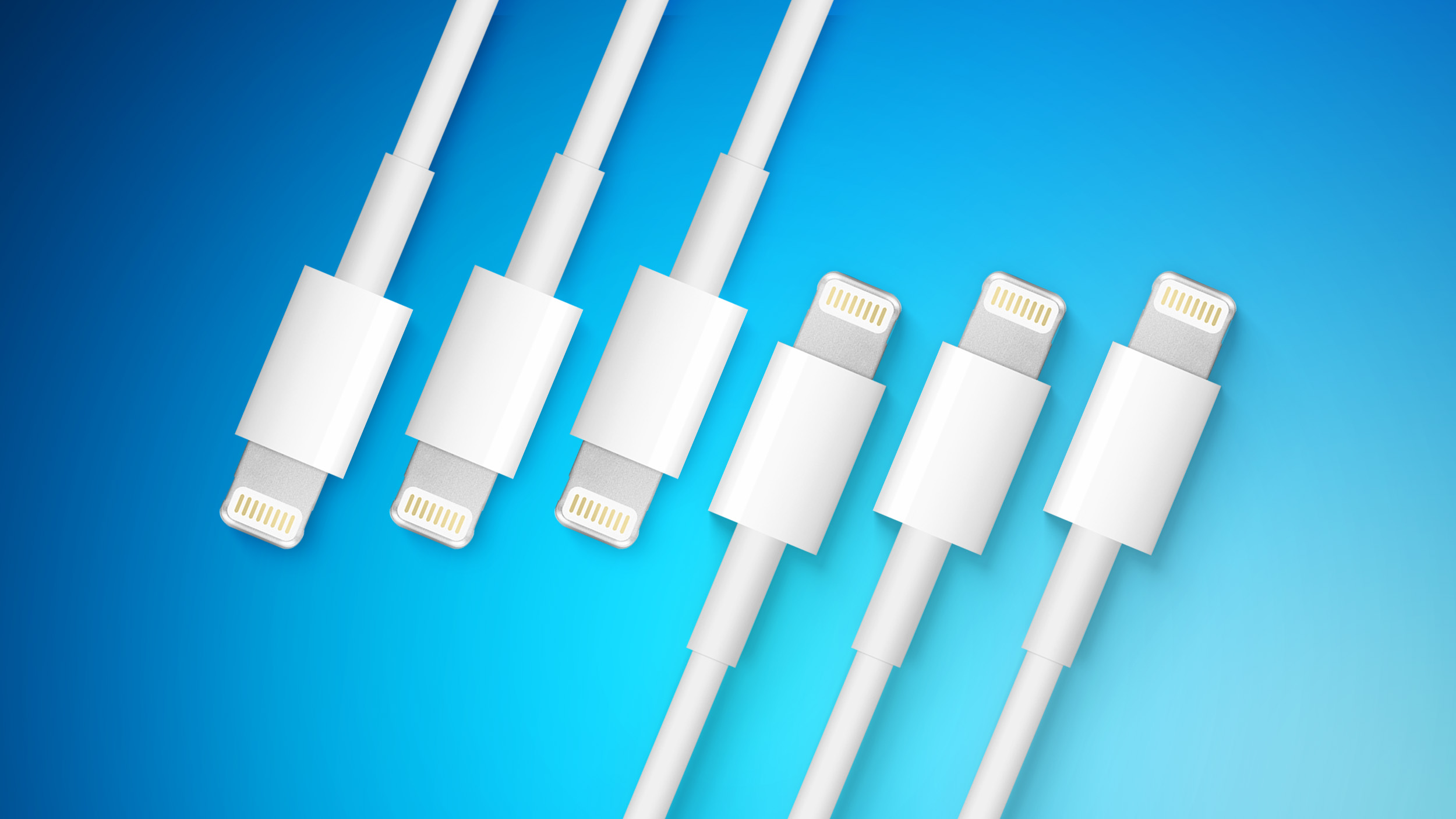
Bad actors have learned to use public USB ports to “introduce malware and monitoring software onto devices,” the FBI said. When out in public, users should bring their own charger and USB cord, using an electrical outlet for charging purposes instead of a public USB port.
Apple’s iPhones and Macs have a USB security feature that prevents the Lightning port from being used for data transfer purposes when it has been more than an hour since the device was unlocked, but this does not prevent malware installation if you are actively using your device and connect to a public port.
Avoid using free charging stations in airports, hotels or shopping centers. Bad actors have figured out ways to use public USB ports to introduce malware and monitoring software onto devices. Carry your own charger and USB cord and use an electrical outlet instead. pic.twitter.com/9T62SYen9T
— FBI Denver (@FBIDenver) April 6, 2023
If a public USB port is used to transfer malware to a computer, tablet, or smartphone, hackers can gain access to sensitive data on the device, siphoning usernames and passwords, hijacking email, stealing money from online accounts, and more.
The only way to stay safe is to use your own USB cable to charge in public spaces, which effectively prevents this potential method of attack.
The FBI has a similar warning on its website, noting that people should not use free charging stations. The FBI also warns against using public Wi-Fi for sensitive transactions, opening suspicious documents, using the same password for all accounts, and clicking unsolicited links in text messages and emails.
This article, “FBI Warns Against Using Public USB Ports Due to Malware Risk” first appeared on MacRumors.com
Discuss this article in our forums
Pinduoduo, a Top Chinese Shopping App, Is Laced With Malware
A researcher used ChatGPT to create dangerous data-stealing malware
IRS-Authorized eFile.com Tax Return Software Caught Serving JS Malware
On March 17th, a Reddit thread surfaced where multiple eFile.com users suspected the website was “hijacked.” At the time, the website showed an SSL error message that, some suspected, was fake and indicative of a hack. Turns out that’s indeed the case. […] The malicious JavaScript file ‘update.js’, further attempts to prompt users to download next stage payload, depending on whether they are using Chrome [update.exe – VirusTotal] or Firefox [installer.exe – VirusTotal]. Antivirus products have already started flagging these executables as trojans.
BleepingComputer has independently confirmed these binaries establish a connection to a Tokyo-based IP address, 47.245.6.91, that appears to be hosted with Alibaba. The same IP also hosts the illicit domain, infoamanewonliag[.]online associated with this incident. Security research group, MalwareHunterTeam further analyzed these binaries, and stated that these contain Windows botnets written in PHP — a fact that the research group mocked. Additionally, the group called out eFile.com for leaving the malicious code on its website for weeks: “So, the website of [efile.com]… got compromised at least around middle of March & still not cleaned,” writes MalwareHunterTeam.
Read more of this story at Slashdot.
E-commerce company with hundreds of millions of users accused of distributing Android malware

Google recently suspended e-commerce giant Pinduoduo’s official Play store app and warned users that several of the company’s other apps contain malware. Pinduoduo’s main Google Play store app (and the Apple App Store’s, for that matter) is likely harmless, but Google said versions from other distribution channels are dangerous.
Google flags apps made by popular Chinese e-commerce giant as malware
On Monday, Google announced that it had flagged several apps made by a Chinese e-commerce giant as malware, alerting users who had them installed, and suspended the company’s official app. In the last couple of weeks, multiple Chinese security researchers accused Pinduoduo, a rising e-commerce giant that boasts almost 800 million active users, of making […]
Google flags apps made by popular Chinese e-commerce giant as malware by Lorenzo Franceschi-Bicchierai originally published on TechCrunch