Tag: unusual
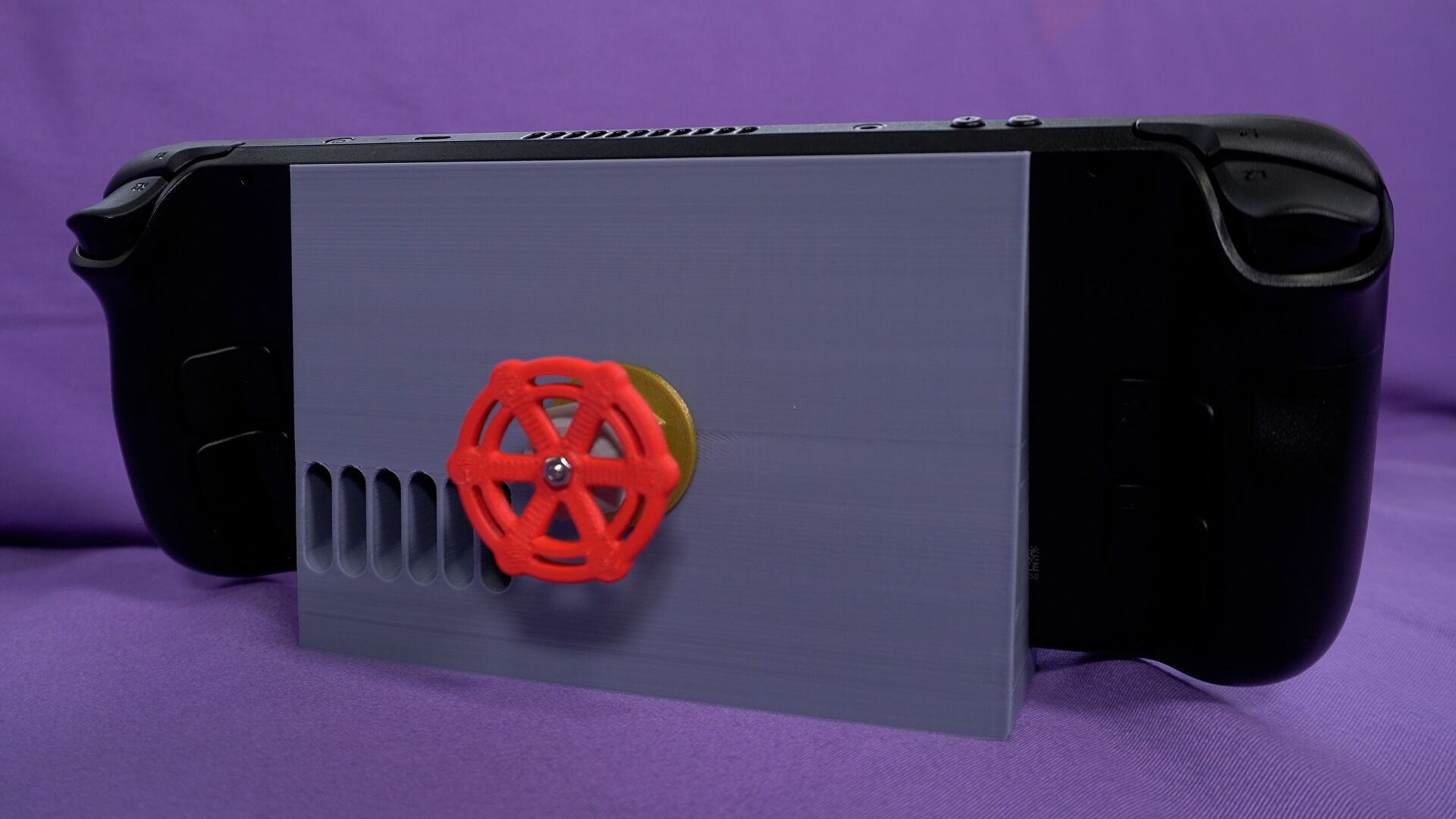
Five unusual Steam Deck accessories – which are the best?
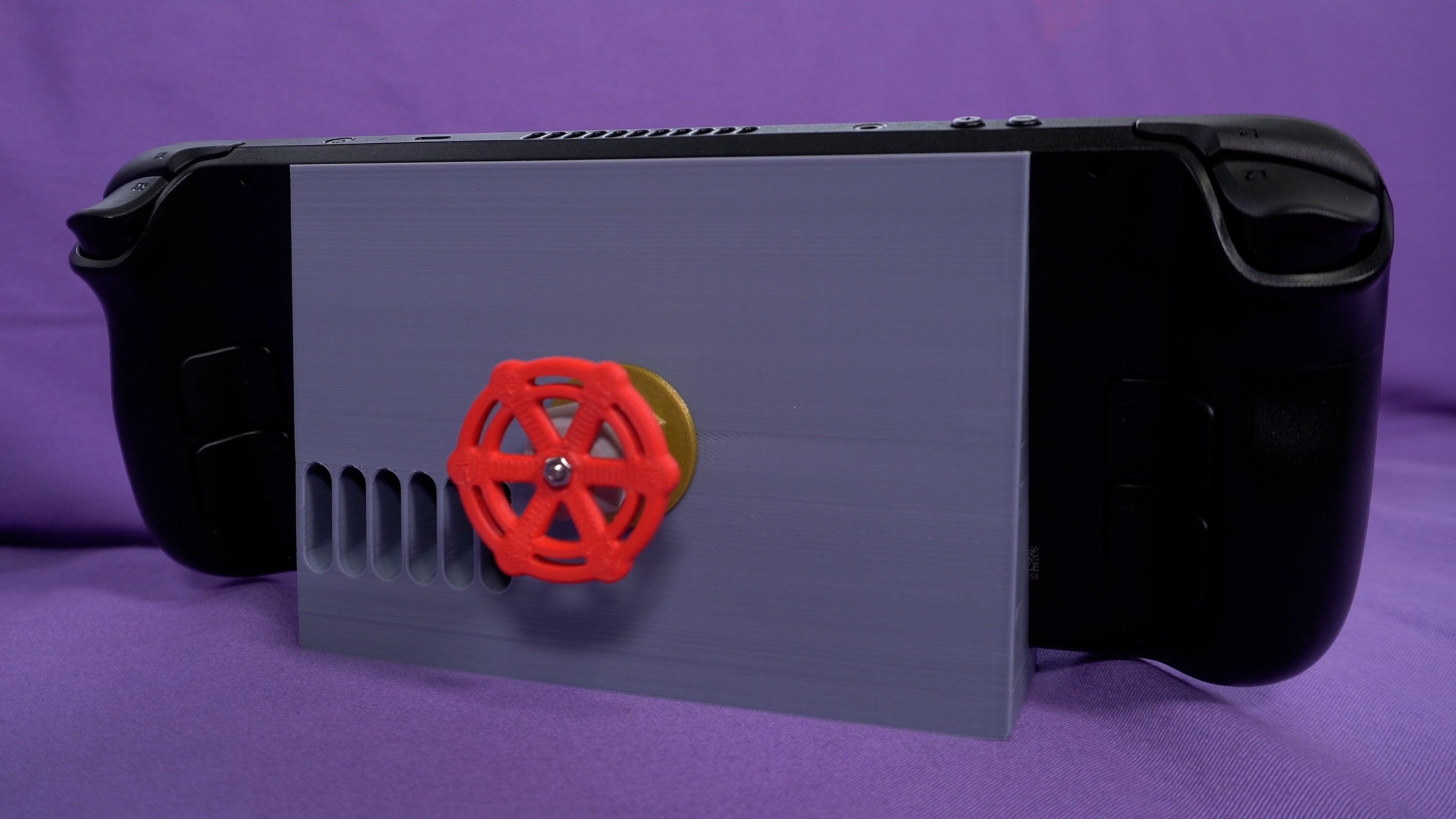
A while back, I was wondering where all the Steam Deck accessories were. Valve themselves have the case covered, including a decent hard case with even the cheapest 64GB models, and it’s not difficult to pick up one of the best microSD cards for the Steam Deck. Otherwise, and especially with delays to Valve’s official dock, there’s not much out there from the usual PC hardware suppliers.
I therefore turned to the makers and sellers of Etsy, where a kind of indie Steam Deck accessory market has emerged. Soon, I’d bought (with my own money, you’re welcome ReedPop) a selection of unique, handcrafted, sometimes questionable gadgets and appendages, and promptly packed them onto a train for independent appraisal by a newly minted Steam Deck owner. Specifically, RPS vid bud Liam.
Powerful New Linux Malware Shikitega Uses Unusual Multi-Stage Stealth
With a rise of nearly 650% in malware and ransomware for Linux this year, reaching an all-time high in the first half year of 2022, threat actors find servers, endpoints and IoT devices based on Linux operating systems more and more valuable and find new ways to deliver their malicious payloads. New malwares like BotenaGo and EnemyBot are examples of how malware writers rapidly incorporate recently discovered vulnerabilities to find new victims and increase their reach.
But they’ve discovered a new malware targetting Linux endpoints and IoT devices, stealthily “delivered in a multistage infection chain where each module responds to a part of the payload and downloads and executes the next one. An attacker can gain full control of the system, in addition to the cryptocurrency miner that will be executed and set to persist.”
The Register summarizes their report:
The malware was dubbed “Shikitega” for its extensive use of the popular Shikata Ga Nai polymorphic encoder, which allows the malware to “mutate” its code to avoid detection. Shikitega alters its code each time it runs through one of several decoding loops that AT&T said each deliver multiple attacks, beginning with an ELF file that’s just 370 bytes… AT&T didn’t say how the initial infection occurs, but it did say Shikitega exploits two Linux vulnerabilities disclosed in 2021 to achieve its ultimate objective, which AT&T said appears to be the installation and execution of the XMRig cryptocurrency miner.
The final stage also establishes persistence, which Shikitega does by downloading and executing five shell scripts that configure a pair of cron jobs for the current user and a pair for the root user using crontab, which it can also install if not available. Shikitega also uses cloud hosting solutions to store parts of its payload, which it further uses to obfuscate itself by contacting via IP address instead of domain name….> >
Bottom line: Shikitega is a nasty piece of code. AT&T recommends Linux endpoint and IoT device managers keep security patches installed, keep EDR software up to date and make regular backups of essential systems.
Ars Technica reports:
The ultimate objective of the malware isn’t clear. It drops the XMRig software for mining the Monero cryptocurrency, so stealthy cryptojacking is one possibility. But Shikitega also downloads and executes a powerful Metasploit package known as Mettle, which bundles capabilities including webcam control, credential stealing, and multiple reverse shells into a package that runs on everything from “the smallest embedded Linux targets to big iron.” Mettle’s inclusion leaves open the potential that surreptitious Monero mining isn’t the sole function….
Given the work the unknown threat actors responsible devoted to the malware’s stealth, it wouldn’t be surprising if the malware is lurking undetected on some systems.
Read more of this story at Slashdot.
Immortality Review – A Most Unusual Camera
There’s a moment in movies where a restless, investigative protagonist falls down a proverbial rabbit hole and unveils a startling truth, reframing everything they thought they knew. The allure of Immortality, much like other games from Sam Barlow and Half Mermaid, is that it casts the player in this exciting role and builds to its ultimate unveiling. It’s borderline impenetrable at times, as both the basic A to B plot and its greater themes are much more opaque than the team’s prior puzzles. And yet, it’s not really worse off for it. Despite–and sometimes because of–the dizzying effect of falling down the rabbit hole, Immortality becomes another standout narrative. It’s similar to its predecessors, Telling Lies and Her Story, in some key ways, but more thought-provoking, too, and certainly more unnerving than you’ll be prepared for.
Writing this review has proven difficult because virtually all of the game feels like a spoiler. I can allude to things, such as the game being scarier than I would’ve guessed, but I can’t really tell you why. I can vaguely mention the story’s dramatic turns, but given the scattered timeline, you may not see certain moments yourself until long after I did. I can at least explain how this game works, because if it’s the first time you’re experiencing a game from this small team, it’s going to feel completely alien.

Playing Immortality is like operating an old-fashioned Moviola machine, once used by editors in filmmaking but now repurposed to let you scrub through hours and hours of vintage live-action movies in an attempt to solve a mystery: What happened to Marissa Marcel? As a fictional 17-year-old actor making her movie debut in late ’60s Hollywood, Marissa was primed to be the Next Big Thing, but over the next 31 years, she would only be cast in three movies, and none of them ever saw release.