Tag: in-app
This site exposes the creepy things in-app browsers from TikTok and Instagram might track

Did you know you’re potentially being tracked when you load an in-app browser on iOS? A new tool reveals exactly how, showing how applications like TikTok and Instagram can potentially use JavaScript to view sensitive data, including your address, passwords and credit card information, without your consent.
The tool can be found at InAppBrowser.com. All you need to do is open the app you want to check and share the InAppBrowser.com URL somewhere within it — such as DMing the link to a friend or posting it in a comment. From there, you can tap the link and get a report from the website on what scripts are running in the background.
…
TikTok denies claims of keystroke monitoring with in-app browser
TikTok’s use of code is the ‘equivalent of installing a keylogger on third-party websites’, according to a privacy researcher. But the company says this code is used for debugging and performance monitoring.
Read more: TikTok denies claims of keystroke monitoring with in-app browser
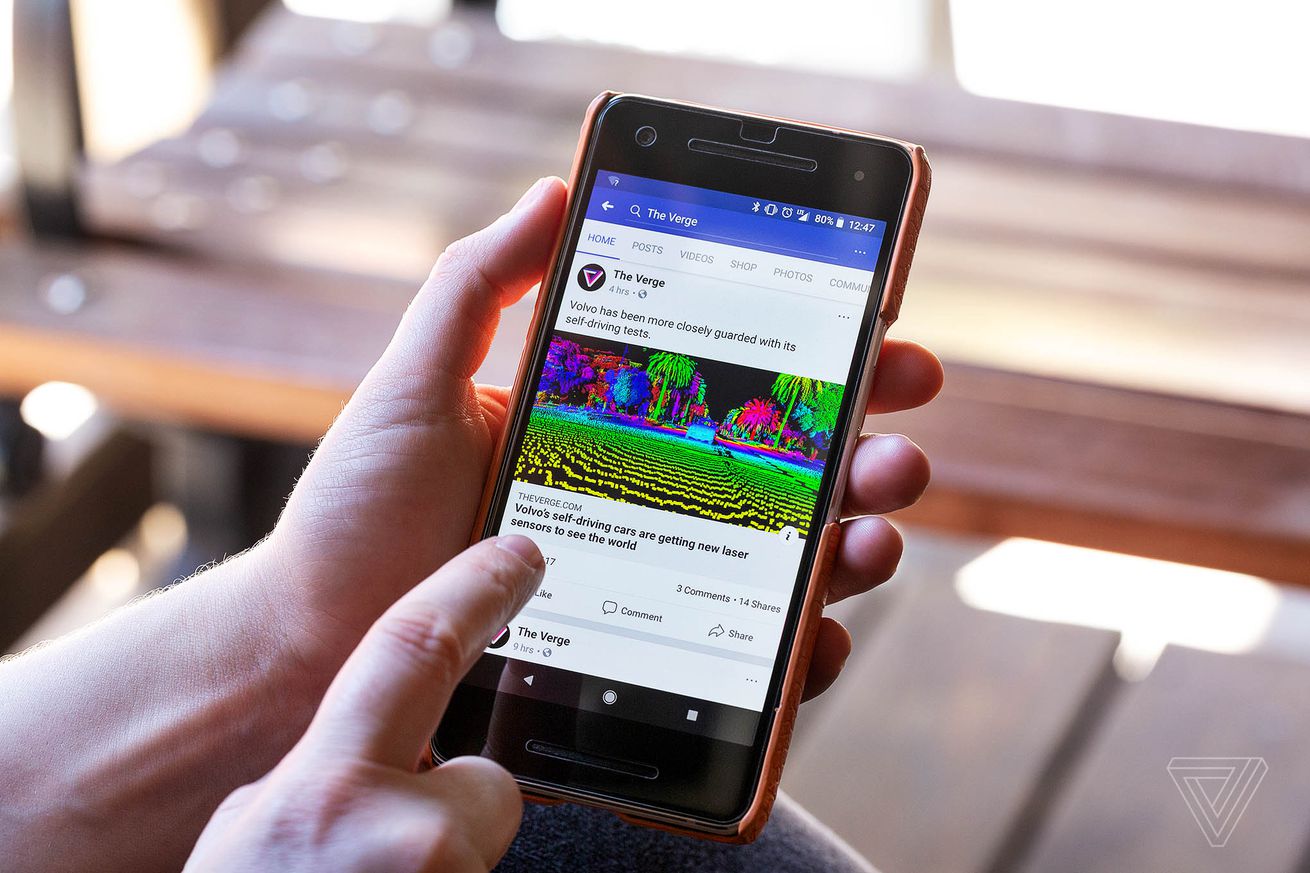
Facebook and Instagram apps can track users via their in-app browsers
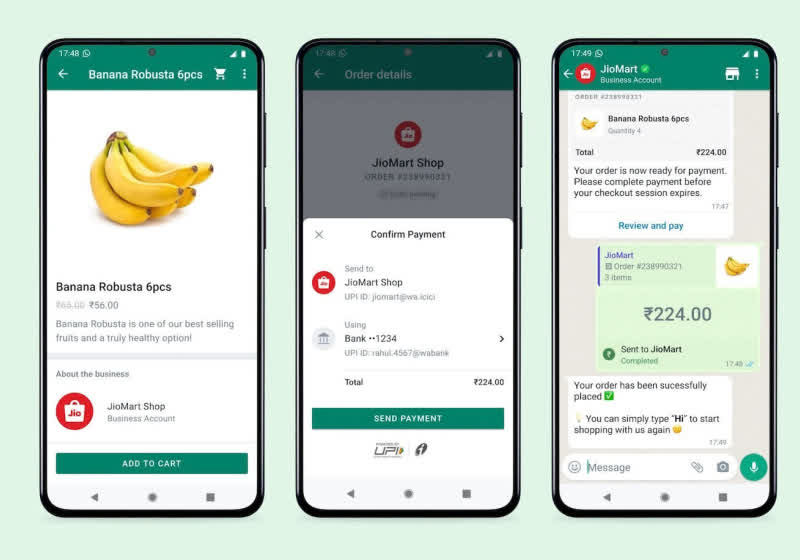
If you visit a website you see on Facebook and Instagram, you’ve likely noticed that you’re not redirected to your browser of choice but rather a custom in-app browser. It turns out that those browsers inject javascript code into each website visited, allowing parent Meta to potentially track you across websites, researcher Felix Krause has discovered.
“The Instagram app injects their tracking code into every website shown, including when clicking on ads, enabling them [to] monitor all user interactions, like every button and link tapped, text selections, screenshots, as well as any form inputs, like passwords, addresses and credit card numbers,” Krause said in a blog post.
His research focused on the iOS versions of Facebook and Instagram. That’s key because Apple allows users to opt in or out of app tracking when they first open an app, via its App Tracking Transparency (ATT) introduced in iOS 14.5. Meta has previously said that the feature was “a headwind on our business 2022… on the order of $10 billion.”
Meta said that the injected tracking code obeyed users preferences on ATT. “The code allows us to aggregate user data before using it for targeted advertising or measurement purposes,” a spokesperson told The Guardian. “We do not add any pixels. Code is injected so that we can aggregate conversion events from pixels. For purchases made through the in-app browser, we seek user consent to save payment information for the purposes of autofill.”
Krause noted that Facebook isn’t necessarily using the javascript injection to collect sensitive data. However, if the apps opened a users’ preferred browser like Safari or Firefox, there would be no way to do a similar javascript injection on any secure site. By contrast, the approach used by the Instagram and Facebook in-app browsers “works for any website, no matter whether it’s encrypted or not,” he said.
According to Krause’s research, WhatsApp doesn’t modify third-party websites in a similar way. As such, he suggests that Meta should do the same with Facebook and Instagram, or just use Safari or another browser to open links. “It’s what’s best for the user, and the right thing to do.” For more, check out the summary of his findings here.